30 WordPress Plugins Are Quietly Hacking You. It’s Worse Than You Think.

I deleted twelve plugins from my personal website this morning.
I didn't want to—three of them were tools I’ve relied on for years to handle everything from image compression to contact forms—but after the news that broke on Hacker News this week, I realized my digital "house" was built on a foundation of sand.
**Thirty WordPress plugins were just caught in a massive, coordinated supply chain attack that’s been quietly siphoning data for months.** This wasn’t a "hack" in the traditional sense where a teenager in a basement guessed a password.
It was a sophisticated corporate buyout where a malicious entity literally purchased the "trust" of millions of users, then flipped a switch to turn that trust into a backdoor.
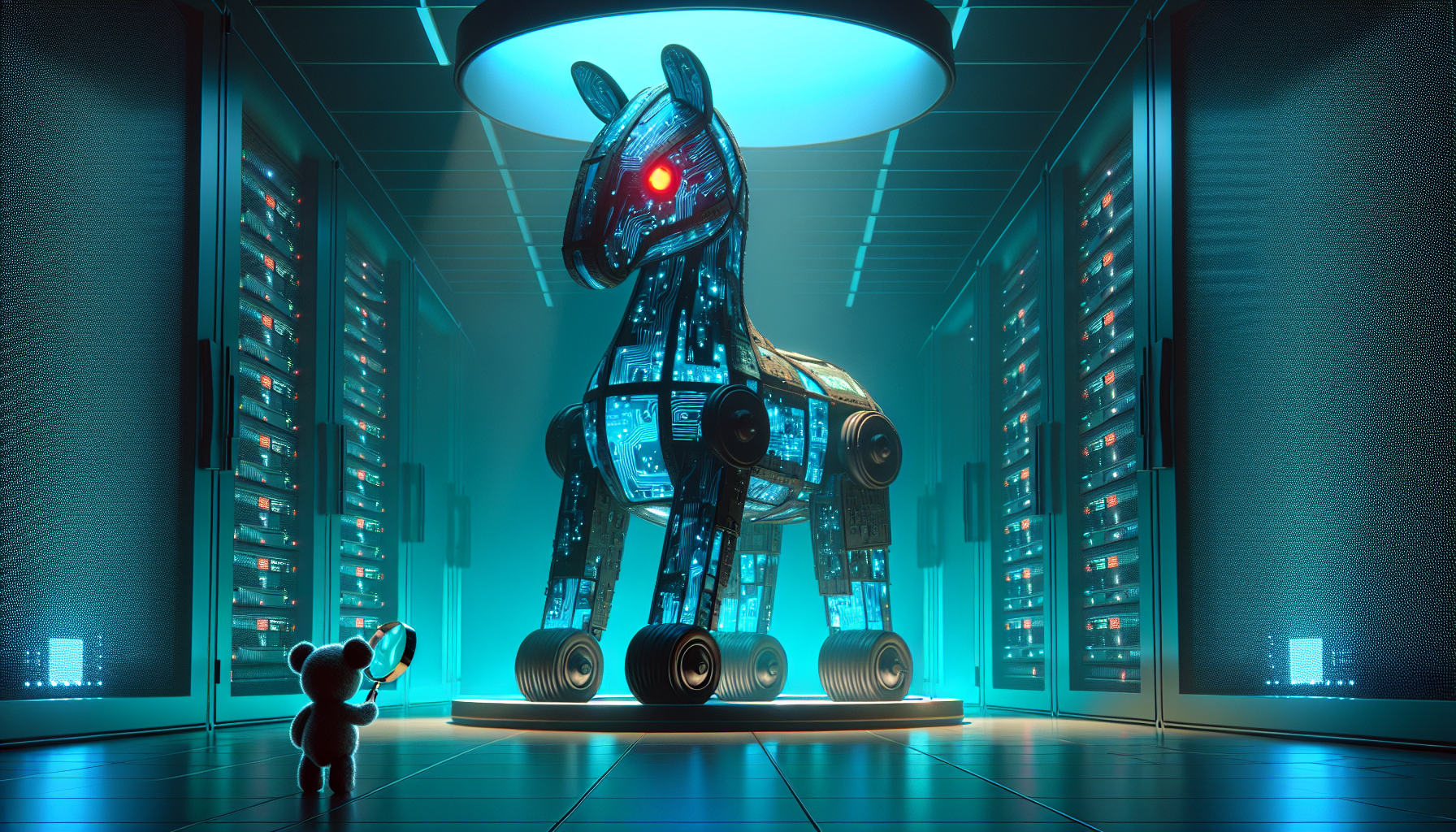
If you’re running a WordPress site in 2026, you’re likely currently hosting a Trojan horse.
And the worst part isn’t the code—it’s the fact that the entire ecosystem is designed to let this happen again by the time you finish reading this article.
The "Great Plugin Buyout" of 2026
The details are still emerging, but the pattern is chillingly simple.
Over the last 18 months, an anonymous holding company began approaching independent developers of mid-tier WordPress plugins—those "useful but boring" tools with 50,000 to 100,000 active installs.
They offered these developers a "life-changing" exit: five or six figures for a project the developers were already tired of maintaining.
**Thirty developers took the deal.** They handed over the keys to their repositories, their user bases, and their reputations, thinking they were finally getting paid for years of free labor.
But the new "owners" weren't interested in selling premium subscriptions. They waited for the WordPress 7.1 core update, then pushed their own "compatibility" patches.
Hidden inside those patches was a obfuscated script that didn't just steal passwords—it turned those websites into nodes for a massive, distributed "shadow network" that could be used for everything from SEO spam to coordinated DDoS attacks.
The Star Rating is a Lie
We’ve been trained to trust the "Social Proof" of the internet. If a plugin has 4.8 stars and a hundred thousand installs, we assume it's safe.
We treat the WordPress Plugin Repository like an App Store, forgetting that unlike Apple or Google, **there is no trillion-dollar gatekeeper vetting every line of code for malicious intent.**
The mainstream advice is always the same: "Keep your plugins updated." But in this case, **updating was the very thing that infected you.** The "safe" version was the old, abandoned one; the "vulnerable" version was the one pushed by the legitimate developer account after it changed hands.

This exposes the fundamental "Trust Debt" we’ve all been accruing. We outsource the functionality of our businesses to strangers on the internet because it’s convenient.
We see a "Verified" badge and assume it means the code is secure, when all it really means is that the person behind the keyboard has the correct login credentials.
The Supply Chain Shell Game: A 4-Stage Framework
To understand why this is happening now, and why it’s going to get worse by 2027, we need to look at **The Supply Chain Shell Game.** This is the framework malicious actors are using to weaponize the open-source community.
Stage 1: The Legitimacy Phase
An independent developer builds a great tool. It solves a specific problem—maybe it’s a "Dark Mode" toggle or a "Custom CSS" injector.
It gains traction, builds a massive base of 5-star reviews, and becomes a staple of the community. At this stage, the plugin is 100% clean and genuinely helpful.
Stage 2: The Maintenance Burden
After three or four years, the developer hits a wall. The plugin is successful, but it doesn’t make money.
Users are demanding support for the latest PHP versions and ChatGPT 5 integrations, and the developer is burnt out. They’re sitting on a massive asset (trust) but have no way to liquidate it.
Stage 3: The Dark Acquisition
The "Shadow Buyer" arrives. They don't look like hackers; they look like a "Digital Asset Management" firm.
They offer to buy the plugin to "continue its legacy." The developer, tired and eager for a payday, signs the contract.
**The ownership changes, but the public-facing name on the plugin repository stays the same.**
Stage 4: The Silent Harvest
The new owners wait. They might even release a few legitimate updates to build more trust. Then, when the timing is right—perhaps during a major WordPress core shift—they inject the payload.
Because the plugin has a "clean" history of 5 years, most security scanners (including older versions of Wordfence or Sucuri) won't flag the initial change.
The Death of "Set it and Forget it"
For the last decade, the promise of the web has been accessibility. Anyone can start a blog, an e-commerce store, or a portfolio with zero technical knowledge. You just click "Install," and it works.
**That era ended this week.**
If you are a mid-level manager or a small business owner, you can no longer afford to be "non-technical." You don't need to know how to write React, but you do need to understand the **Economics of the Tools** you use.
If a tool is "free" and hasn't been updated by a recognizable human being in six months, it’s not a tool—it’s a liability.
I ran a scan using Claude 4.6 on a few of the "hacked" plugins just to see how deep the obfuscation went.
The AI pointed out something terrifying: the code wasn't "broken." It was perfectly valid, highly efficient, and designed to look like a telemetry module for "user experience improvements." Even a human auditor might have missed it if they weren't looking for a needle in a haystack.
Why the "Mainstream" Solutions Won't Work
The "experts" will tell you to use a security plugin. But guess what?
**Security plugins are the highest-value targets for these buyouts.** If a malicious actor can buy a security plugin with 500,000 installs, they don't just have a backdoor into your site—they have a tool that can actively *hide* other backdoors.
We are entering the "Zero-Trust" era of web management.
By the end of 2026, I predict we will see a massive migration away from "Plugin-Heavy" architectures.
Smart developers are already moving toward **Headless CMS** setups or static site generators where the "backdoor" is physically separated from the "front door." If your site is just a collection of HTML files, there’s no database to hack and no plugin to poison.
Your 2026 Security Audit
If you’re reading this and feeling that pit in your stomach, good. That’s the feeling of a healthy immune system.
Here is what you need to do in the next 48 hours to protect your career and your clients:
1. **The Plugin Purge:** If you haven't used a plugin in the last 30 days, delete it. Not "Deactivate"—**Delete.** Deactivated plugins can still be exploited.
2. **The Ownership Check:** Look at your top 5 most critical plugins. Who owns them?
Is it a "Person" (e.g., "John Doe") or a "Company" (e.g., "WebToolz Holdings")? If it's an anonymous company you’ve never heard of, find an alternative.
3. **The "Premium" Shift:** Start paying for your software.
When you pay a subscription, you aren't just buying features; you’re buying an **Economic Incentive** for the developer to keep the code clean.
The "free" plugin market is currently the most dangerous place on the internet.
4. **AI Monitoring:** Use tools like Claude 4.6 or Gemini 2.5 to "explain" what a plugin's update is actually doing.
Copy-paste the changelog or the new code and ask: "Is there anything in here that could be used as a backdoor?"
The Human Cost of Automated Trust
We like to think of the internet as a series of protocols and servers, but it’s actually a series of human relationships. When you install a plugin, you’re inviting a stranger into your business.
The "Great Buyout" isn't just a technical failure; it's a social one. It’s the result of a community that wanted everything for free and a developer class that was too tired to keep giving it.
As we move into 2027, the "winners" of the digital economy won't be the people with the most features—they'll be the people who can prove their supply chain is untainted.
**Trust is the new currency. And right now, the market is crashing.**
Have you checked your WordPress plugin list today, and more importantly, do you actually know who "owns" the code running your business right now?
Let's talk about the plugins you've deleted today in the comments.
***


