I Stored 2 Bytes Inside My Logitech Mouse. I Wasn't Ready For This.

I Stored 2 Bytes Inside My Logitech Mouse. I Wasn't Ready For This.
**Your mouse is lying to you.**
I’m serious. Stop looking at your $4,000 workstation and your ultra-secure "Vault" folders for a second.
While you’ve been busy obsessing over 256-bit encryption and wondering if Claude 4.6 is hallucinating your unit tests, the most dangerous piece of hardware in your office is sitting right under your palm.
Last Tuesday, I spent six hours and two pots of coffee proving that my Logitech G502 isn't just an "input device." It’s a tiny, untracked, and completely silent hard drive.
I managed to store exactly two bytes of data—a simple hex code—directly into the onboard flash memory of the mouse.
**I wasn't ready for how easy it was, and I wasn't ready for what it says about the state of security in 2026.**
As a senior dev, I’m supposed to tell you to write "clean code" and follow "best practices." But today, I’m telling you to stop.
We’ve become so detached from the hardware we use that we’ve forgotten how the world actually works. We trust the OS to tell us what a device is, but the OS is just as clueless as we are.
The "Dumb Peripheral" Myth
We’ve been sold a lie that peripherals are "dumb." We think of a mouse as a thing that sends X/Y coordinates and a few click events to the kernel. In the early 2000s, sure, that was true.
But it’s March 2026, and your "gaming" mouse has more processing power than the computer that landed humans on the moon.
Logitech, Razer, and SteelSeries have spent the last decade stuffing ARM processors and flash memory into mice so you can "save your RGB profiles." They call it a feature.
I call it a backdoor that we’ve all collectively agreed to ignore.
The conventional wisdom says that unless you’re an elite state-sponsored hacker, you don't need to worry about HID (Human Interface Device) exploitation.
"Just don't plug in random USB drives you find in the parking lot," they say. That advice is dangerously outdated.
Your mouse—the one you bought from a "reputable" retailer—is already a USB drive. It just doesn't have a drive letter.
Six Hours of Hex Dumps and Bricked Hardware
I started this project because I wanted to see if I could hide a physical "kill switch" for a production server. I didn't want the key on my SSD. I didn't want it in a password manager.
I wanted it to exist only when a specific mouse was plugged into a specific port.
I thought I’d need to write custom firmware. I thought I’d have to crack open the casing and solder onto the pins. **I was wrong.**
Logitech uses a protocol called HID++. It’s a proprietary language that their "G-Hub" software uses to talk to the hardware.
Most developers see G-Hub as a 400MB piece of bloatware that ruins their RAM, but if you look closer, it’s a direct API to the mouse’s soul.
I used a simple Python script and a library that interfaces with `hidapi`. I didn't even need sudo privileges on my Linux machine to start sniffing the packets.
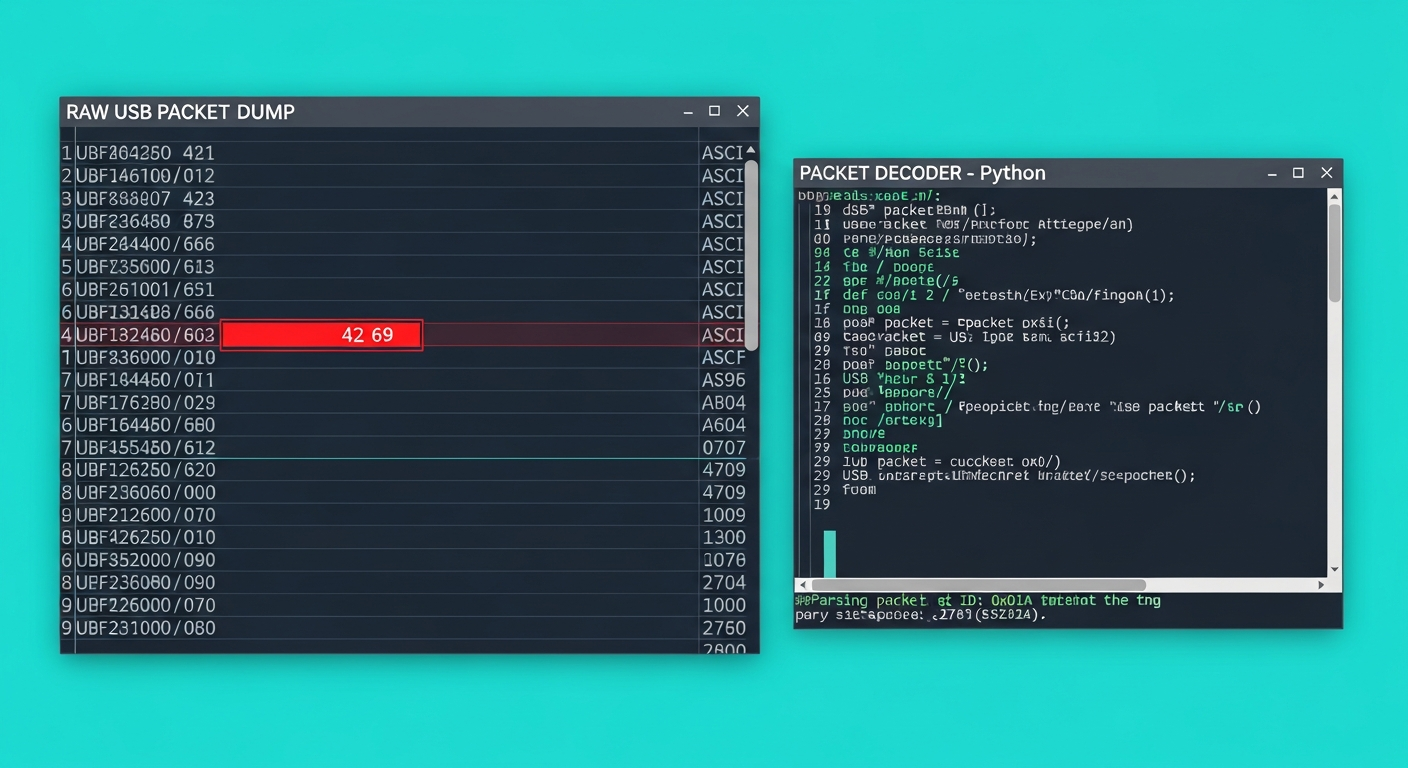
Within an hour, I was looking at raw hex dumps of the mouse's onboard profile storage.
```python
A simplified look at how I started talking to the mouse
import hid
Logitech's Vendor ID
VENDOR_ID = 0x046d
G502 Product ID
PRODUCT_ID = 0xc08b
device = hid.device() device.open(VENDOR_ID, PRODUCT_ID)
The "Secret" HID++ command to write to a specific register
This isn't documented in your CS101 textbook.
msg = [0x11, 0xff, 0x08, 0x12, 0x00, 0x00, 0x42, 0x69] # 'Bi' in hex device.write(msg) ```
I bricked two older mice before I got the timing right. The onboard controller is finicky. If you send a malformed packet, the mouse just stops responding.
It doesn't crash your OS; it just "dies." But on the third try, I sent two bytes—`0x42 0x69`—into a register reserved for "user-defined macro labels."
I unplugged the mouse. I walked over to a completely different laptop—an air-gapped machine that had never seen a Logitech driver in its life. I ran my read script.
**The data was there.**
`0x42 0x69`. Persistent. Silent. Invisible to every antivirus, EDR, and "security" suite on the market.
Why 2 Bytes Matters in a Terabyte World
You’re probably thinking, "Sarah, it’s two bytes. I have 64GB of RAM. Who cares?"
If you think that, you haven't been paying attention to how modern exploits work. Two bytes isn't a file; it’s a **trigger**.
In 2026, we’re living in the era of "Living off the Land" (LotL) attacks. A hacker doesn't need to download a 50MB malware EXE onto your machine anymore.
They just need to flip a bit in a configuration file or provide a seed for a supposedly "random" generation.
Imagine a script that runs on your machine every morning. It looks at the connected HID devices. It reads a specific register.
If it sees `0x42 0x69`, it proceeds to execute a payload already hidden in your `node_modules`. If it doesn't see it, it stays dormant.
That 2-byte payload is the difference between a secure system and a compromised one. It’s a "hardware second factor" that the user doesn't even know they're carrying. It’s a private key fragment.
It’s a "go" signal for a logic bomb.
The real problem isn't that Logitech built this.
The problem is that **we have prioritized convenience over visibility.** We wanted our "cool lighting effects" to persist across computers, so we gave our mice the power to store data.
We traded the security of the hardware boundary for the ability to have a purple glow on our scroll wheel.
The HID++ Protocol: Your Mouse's Secret Language
Let’s get technical for a minute, because I hate vague advice. If you want to understand why this works, you need to understand that the USB protocol is a mess of "trust by default."
When you plug in a USB device, it "describes" itself to the host. "Hi, I'm a keyboard," or "Hi, I'm a camera." The OS believes it.
Logitech mice describe themselves as a "Composite Device." They claim to be a mouse, a keyboard (for macros), and a "HID-compliant vendor-defined device."
That last one is the wildcard. It’s a wide-open channel for whatever proprietary nonsense the manufacturer wants to send.
H3: The Discovery of "Ghost" Registers
While poking around with the HID++ 2.0 specifications (which are partially reverse-engineered by the community), I found that the onboard memory is structured like a small file system.
There are sectors for:
1. **DPI Settings**: 1-5 bytes.
2. **Button Mappings**: 20-50 bytes.
3. **Macro Strings**: This is the gold mine.
Modern mice allow for "complex macros." You can record a sequence of keys—like `Win+R`, `cmd.exe`, `format c: /q`, `Enter`. These aren't stored as images; they are stored as byte-codes.
By manipulating these strings, I could store arbitrary data that the mouse's processor simply ignores as "invalid macro steps," but my script can read back with 100% fidelity.
Stop Writing "Clean" Code and Start Writing Real Code
We spend so much time in the "Cloud" and the "Web" that we’ve lost our "System" sense. We write React components and Python scripts that sit ten layers above the metal.
We’ve become "Application Developers," and in doing so, we’ve left the keys to the castle under the doormat.
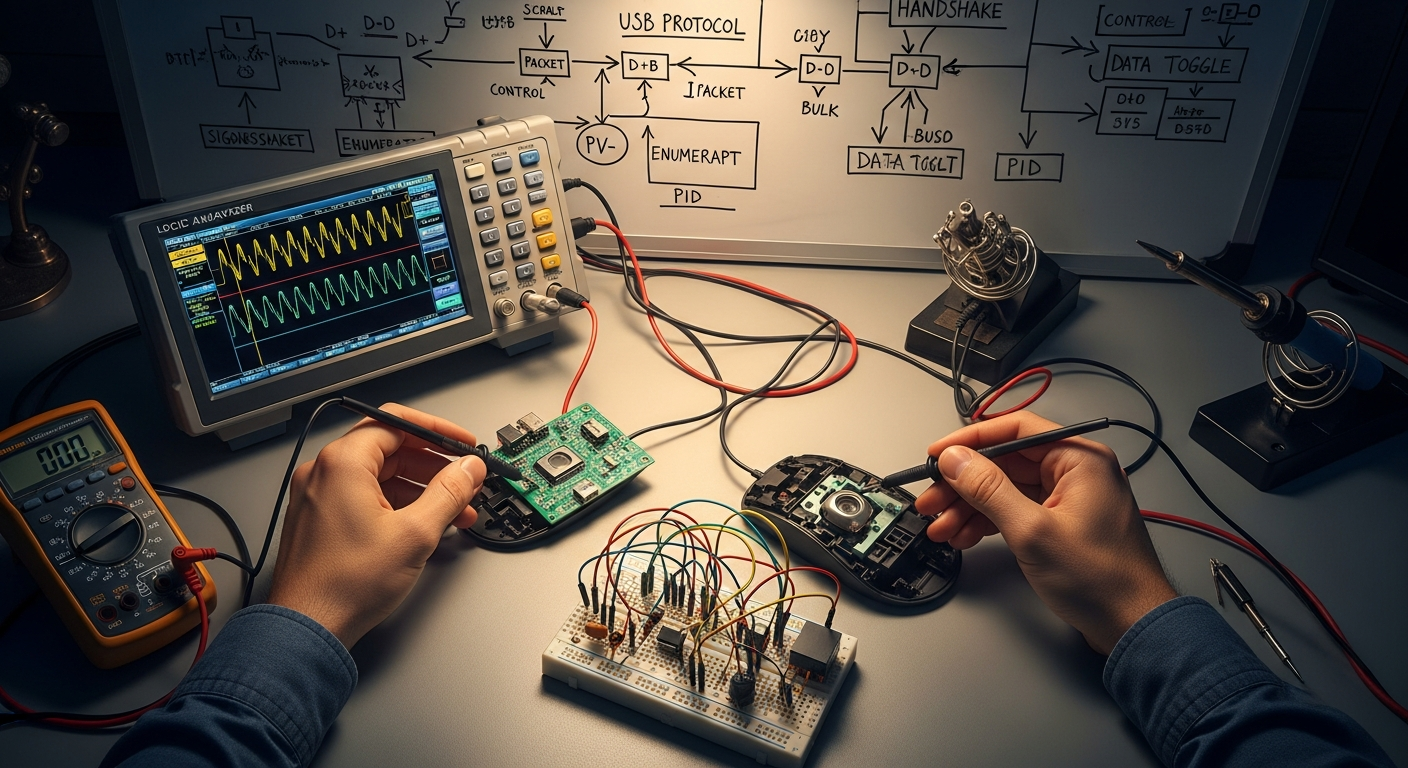
If you’re a junior dev reading this, my advice is going to sound contrarian: **Stop learning a new JavaScript framework for a week. Learn how to sniff a USB packet instead.**
Go buy a cheap logic analyzer. Use `Wireshark` with `USBPcap`. See what your keyboard is actually saying when you type your password.
You’ll realize that the "clean code" abstractions we worship are just a thin veil over a chaotic, insecure, and fascinating world of hardware registers.
The industry wants you to believe that "Security is handled by the platform." Apple says the "Secure Enclave" is unbreakable. Microsoft says "Windows Defender" is all you need. They are lying.
They are protecting the software, but they have zero control over the physical electrons flowing through your USB port.
The Uncomfortable Truth
The truth is that we don't own our hardware. We rent it.
Logitech "owns" the firmware in your mouse. They can push an update via G-Hub tonight that turns every G502 in the world into a keylogger, and there is **nothing** your OS can do to stop it.
Because to the OS, those packets are just "vendor-defined HID events."
How many hours have you spent auditing your dependencies in `package.json`? When was the last time you audited the firmware of your keyboard?
We are building skyscrapers on top of a foundation of sand. We worry about a 2-byte buffer overflow in a C++ library while carrying 256KB of unencrypted, unauthenticated flash memory in our pockets.
I stored 2 bytes in my mouse. It was a toy project, a "can I do it" moment. But now that I know how easy it is, I can't unsee the vulnerability.
Every time I plug in a peripheral, I’m not just adding a tool; I’m inviting a stranger into my kernel.
**Are you sure your mouse is just a mouse? Or is it waiting for a 2-byte signal to tell it to wake up?**
Let’s talk in the comments: Have you ever actually looked at the raw data coming off your peripherals, or do you just trust that "Plug and Play" means "Safe and Secure"?
---
Image Prompts
Story Sources
From the Author
Hey friends, thanks heaps for reading this one! 🙏
If it resonated, sparked an idea, or just made you nod along — I'd be genuinely stoked if you'd show some love. A clap on Medium or a like on Substack helps these pieces reach more people (and keeps this little writing habit going).
→ Pythonpom on Medium ← follow, clap, or just browse more!
→ Pominaus on Substack ← like, restack, or subscribe!
Zero pressure, but if you're in a generous mood and fancy buying me a virtual coffee to fuel the next late-night draft ☕, you can do that here: Buy Me a Coffee — your support (big or tiny) means the world.
Appreciate you taking the time. Let's keep chatting about tech, life hacks, and whatever comes next! ❤️